What Anthropic’s Claude for Legal Means for Law Firms
Anthropic’s launch of Claude for Legal signals a major shift in how law firms will use AI. With deep integrations into the platforms firms already rely on, legal AI is moving beyond standalone tools into connected, practice-aware workflows. But as firms embrace these capabilities, security, governance, and implementation strategy will be critical to getting it right.

NetDocuments Unveils the First Context Graph for Legal Work and a Reimagined Platform Built Around It
As a NetDocuments Diamond partner Element, recognizes what NetDocuments is launching today is reshaping how we think about delivering AI-powered legal solutions to our clients.
The Legal Context Graph goes beyond a typical update. It brings together context, institutional knowledge, and governance in a way that connects legal professionals to the information already living across their organization, making it more actionable and more impactful.
At Element, this aligns directly with how we help clients unlock smarter, more connected legal workflows.

AI Just Got a Major Upgrade in Cybersecurity — And Our Clients Are Already Protected
On Monday, April 7 Anthropic announced Claude Mythos Preview, and it's a landmark moment for both artificial intelligence and cybersecurity. As an Element team, we want to make sure you understand what this means — and why our strategic partnership with CrowdStrike puts our clients in a strong position.

Case Study: Delivering World-Class Identity Security at Scale
In this Element Technologies case study, learn how a law-firm-focused MSP standardized Okta delivery and cut new-tenant setup time with ZeroConfig.
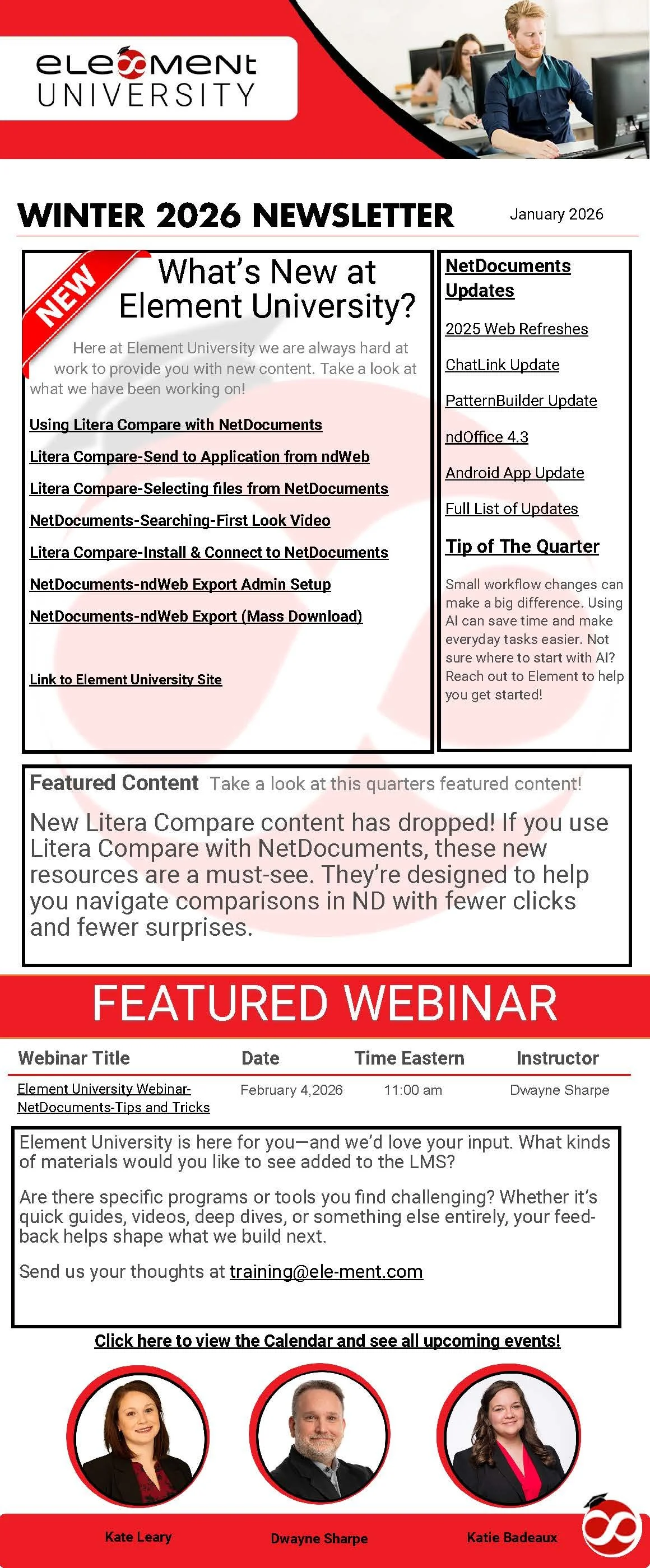
Element University Winter 2026 Newsletter
The Element University Winter 2026 Newsletter is here!
Get the latest updates, resources, and upcoming webinars from Element. Stay connected and keep growing with us.
The Quiet Lever: How Data Privacy Protects Your Whole Life
Data privacy today isn’t just about protecting sensitive information. It’s about managing predictive data, the kind that can quietly influence pricing, access, and opportunities without your knowledge.
When privacy gets sloppy, the impact shows up in real life: financial risk, reputation damage, and decisions shaped by data you never see.
This Data Privacy Day & Week, we’re sharing a deeper look at why privacy is the quiet lever protecting your whole life.

WatchGuard Critical Vulnerability Affecting Fireware OS
WatchGuard has disclosed a critical vulnerability (CVE-2025-14733, CVSS 9.3) affecting Fireware OS on Firebox appliances, with active exploitation reported. We are validating if this applies to your devices and will immediately patch to the latest fixed Fireware OS version.

Getting a New Phone This Holiday Season? Don’t Forget Your MFA Apps!
Getting a new phone for Christmas should feel exciting, not stressful. By taking a few extra minutes to migrate your MFA apps, you’ll set yourself up for a secure and seamless start when you're back to business after the holidays.

Cloudflare Global Network Experiencing Issues
This morning Cloudflare Global Network announced they are experiencing issues. Here is their latest update.

Element Technologies Honored for Award-Winning Partnership with NetDocuments
Element Technologies is proud to receive NetDocuments’ Inspire award for 2025 Implementation Partner of the year and 2025 Strategic Law Partner of the Year!

Element University Fall 2025 Newsletter
What’s New at Element University?
Here at Element University we are always hard at work to provide you with new content. Take a look at what we have been working on!

How a Leading IP Firm Streamlined Automated Processes and Boosted Efficiency with NetDocuments
We’re excited to share how MBHB (McDonnell Boehnen Hulbert & Berghoff LLP) partnered with Element Technologies, LLC and NetDocuments to streamline workflows, automate critical processes, and unlock thousands of hours in time savings.

Security Update for WatchGuard Firebox Devices
WatchGuard has announced a critical security update for Firebox appliances. While there’s no evidence this issue has been exploited, we’re already reviewing all client systems and preparing updates to ensure continued protection.
Your security is our top priority — and we’ve got it covered.

CBS Interviews Element Technologies’ CTO, Craig Sixta, on the Rising Threat of Cyberattacks in Minnesota
Element Technologies’ CTO, Craig Sixta, recently appeared on CBS/WCCO News to discuss the cyberattack on the City of St. Paul and the growing threat of ransomware groups. He shared insights on why these attacks are so hard to stop, the impact of Minnesota’s new cyber reporting law, and how one phishing email can lead to a major breach.

Element Technologies, LLC Named to 2025 Channel Partners MSP 501 List – Recognized Among World’s Top Managed Service Providers
Element Technologies, LLC has been named one of the top-performing managed service providers in the world, earning a spot on the prestigious 2025 Channel Partners MSP 501 list. The annual ranking identifies the best of the best in the managed services industry, based on a range of criteria including revenue growth, recurring revenue, service innovation, and operational efficiency.

World Password Day: Simple Steps to Strengthen Your Digital Security
Each year on the first Thursday of May, World Password Day reminds us of a simple truth: strong passwords are a critical building block of cybersecurity. From your email to your bank account, passwords are the first line of defense for your personal and professional information.

What Is The Cloud, Really? And How Do You Keep It Safe?
The cloud isn’t magic—it’s just someone else’s computer.
So how do you make sure your data stays safe up there?
In our latest blog, we break down what the cloud really is and share 5 easy, practical ways to boost your cloud security—for home or business.

Exciting Updates for Microsoft 365 Copilot & Teams Phone Pricing!
Flexible billing for Microsoft 365 Copilot; pricing updates for annual subscriptions and Teams Phone.

New Charter Technologies Expands National Presence and Service Offerings with Addition of Element Technologies
New Charter Technologies, is excited to announce the addition of Element Technologies to its growing platform of elite managed service providers (MSPs).

LegalRM announces strategic partnership with Element Technologies to support growth in iCompli adoption.
LegalRM announces strategic partnership with Element Technologies to support growth in iCompli adoption.
